Ecommerce: How These Brands Balance Customer Needs with Large...
By Miva
Learn how two ecommerce brands balance a massive catalog with a user-friendly experience to grow sales.
Read Blog

Boost Efficiency: Streamlining Large Ecommerce Catalog Product...
By Miva
Catalog updates causing delays? This post shares efficient hacks to streamline the process and boost sales.
Read Blog

High SKU FAQ: We Tackle the Biggest Questions in Catalog...
By Miva
Your ecommerce platform needs to be equipped to handle the complexity of an extensive catalog. But where do we even begin?
Read Blog
New
 4 minute read
4 minute read
Searchspring: Leveraging Personalization to Boost Conversions...
By Brennan Heyde
Learn how Searchspring's personalization engine allows you to show the right products to the right customers and deliver the ultimate shopping experience.
Read Blog
 3 minute read
3 minute read
How to Plan for Ecommerce Success in the New Year—Top Priorities
By Vanessa Loughty
Focus on these key areas to grow your business in the new year.
Read Blog
 3 minute read
3 minute read
The Most Economical Way to Drive More Ecommerce Traffic to Your...
By Tom Wintaugh
Try this goldmine for generating ecommerce traffic by drawing more traffic to your site.
Read Blog
 3 minute read
3 minute read
Scalable Ecommerce: Main Challenges That Arise When Scaling Up
By Tom Wintaugh
Watch out for these common "growing pains" around scaling your business.
Read Blog
 3 minute read
3 minute read
The Art of the Ecommerce Landing Page: Pages That Drive Purchases
By Vanessa Loughty
Learn the most important elements of an effective ecommerce landing page.
Read Blog
 3 minute read
3 minute read
Selling In Style: Conversion-Focused Ecommerce Copywriting
By Tom Wintaugh
Infuse your copy with these best practices to drive more conversions and share the story of your brand.
Read Blog
 3 minute read
3 minute read
Year-End Check-in: How Did Your Ecommerce Growth Strategy...
By Tom Wintaugh
Ask these 9 questions to gauge how well your growth plan is working.
Read Blog
 3 minute read
3 minute read
How to Use Categories and Subcategories to Improve Product...
By Vanessa Loughty
Organize products to make it easy for customers to find exactly what they're looking for.
Read Blog
 4 minute read
4 minute read
How to Optimize Your Ecommerce Value Proposition
By Tom Wintaugh
Hone your value prop to give customers an irresistible reason to shop at your store.
Read Blog
 3 minute read
3 minute read
Ecommerce Pricing Strategies That Boost Sales and Protect Margins
By Vanessa Loughty
Choose a pricing model that helps you stay competitive, profitable, and aligned with brand value.
Read Blog
 3 minute read
3 minute read
Post-Holiday Ecommerce Strategy: How to Keep Customers Coming...
By Vanessa Loughty
Keep the sales momentum going when seasonal traffic slows down.
Read Blog
 3 minute read
3 minute read
5 Ways to Reduce Checkout Friction
By Tom Wintaugh
Reduce checkout confusion and give your customers more reasons to complete their purchases.
Read Blog
 3 minute read
3 minute read
How Can Ecommerce Merchants Get Products Listed by ChatGPT?
By Tom Wintaugh
As consumers begin turning to AI for product recommendations, how can merchants get their products noticed?
Read Blog
 3 minute read
3 minute read
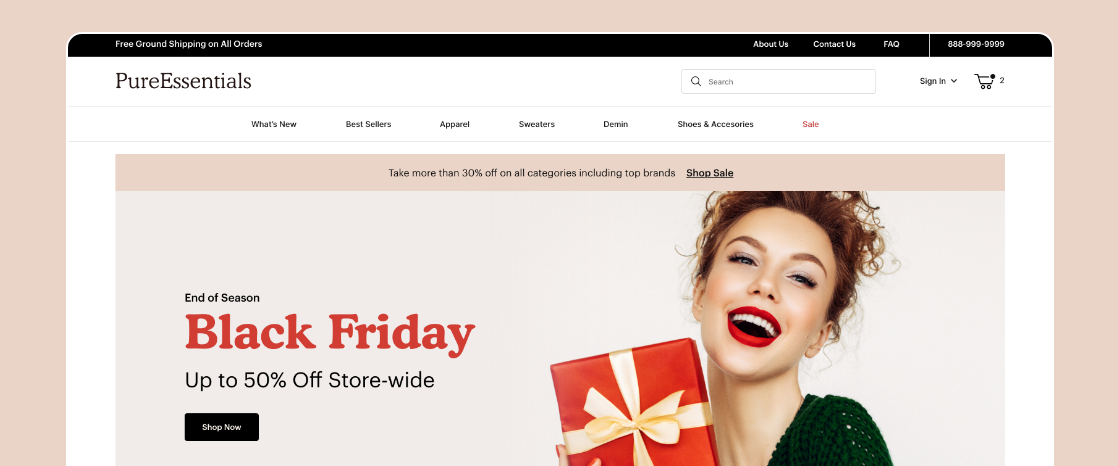
Common Black Friday Mistakes
By Vanessa Loughty
Avoid these holiday sale season pitfalls and boost your Black Friday results.
Read Blog
 3 minute read
3 minute read
How to Write the Perfect Abandoned Cart Email
By Tom Wintaugh
Learn how to lower your customer churn and retain B2B buyers for the long haul.
Read Blog
Subscribe